Business Cybersecurity Solutions: A Comprehensive Protection Strategy for 2025
In today's digital landscape, protecting your business from cyber threats is more critical than ever. This comprehensive guide provides strategies and solutions for implementing robust cybersecurity measures to safeguard your business against evolving threats.
Understanding Modern Cybersecurity Challenges
Modern businesses face increasingly sophisticated cyber threats that require comprehensive security solutions. A robust cybersecurity strategy is essential for protecting sensitive data, maintaining customer trust, and ensuring business continuity.
Key Components
- Network Security: Implementing robust network protection measures to prevent unauthorized access and data breaches.
- Data Protection: Securing sensitive business and customer data through encryption and access controls.
- Access Control: Managing user permissions and authentication to ensure only authorized individuals can access sensitive information.
- Threat Detection: Identifying and responding to security threats in real-time to minimize potential damage.
- Incident Response: Managing and mitigating security incidents effectively to reduce downtime and data loss.
Implementing Enterprise Security Solutions
Developing a comprehensive enterprise security strategy involves integrating various security measures to protect your business from cyber threats. Consider the following components:
1. Security Framework Design
Designing a security framework involves establishing policies, procedures, and controls to protect your business from cyber threats. This includes implementing industry-standard security frameworks such as NIST or ISO 27001.
2. Cybersecurity Implementation
Implementing cybersecurity measures involves deploying technologies and practices to protect your business from threats. This includes firewalls, intrusion detection systems, and encryption tools to secure data and networks.
3. Business Security Strategy
Developing a business security strategy involves aligning security measures with business objectives to ensure comprehensive protection. This includes conducting risk assessments, establishing security policies, and implementing training programs to enhance security awareness.
Practical Application of Business Cybersecurity Solutions
To apply business cybersecurity solutions in your business context, consider the following scenarios:
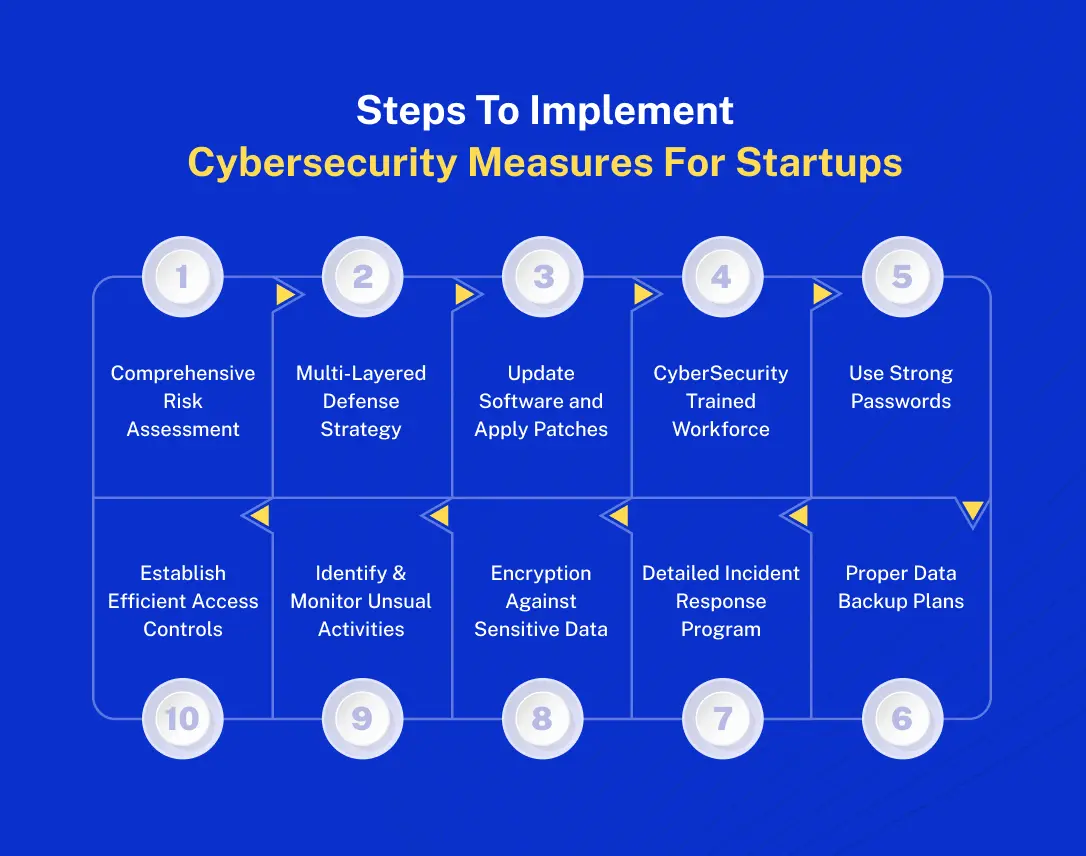
- Startups: Implement robust cybersecurity measures to protect sensitive data and build customer trust from the outset.
- Established Enterprises: Integrate comprehensive cybersecurity solutions to enhance security, comply with industry regulations, and mitigate risks.
Practical Considerations
- Regular Audits: Conduct regular security audits to identify vulnerabilities and ensure compliance with industry standards.
- Employee Training: Provide ongoing training for employees to enhance security awareness and reduce human error.
- Incident Response Plan: Develop and test an incident response plan to ensure effective management of security incidents.
Challenges and Solutions in Business Cybersecurity
Challenge Category 1: Evolving Threats
- Challenge Description: Cyber threats are constantly evolving, making it challenging to stay protected.
- Solution Approach: Implement advanced threat detection and response measures to identify and mitigate emerging threats.
- Practical Tip: Stay informed about the latest cyber threats and update security measures accordingly.
Challenge Category 2: Compliance
- Challenge Description: Ensuring compliance with industry regulations and standards can be complex.
- Solution Approach: Implement robust compliance management practices to ensure adherence to regulatory requirements.
- Practical Tip: Conduct regular compliance audits and updates to stay current with industry standards.
Future Trends in Business Cybersecurity
Emerging Trend 1: AI-Driven Security
AI-driven security solutions utilize artificial intelligence to enhance threat detection and response capabilities, providing more robust protection against cyber threats.
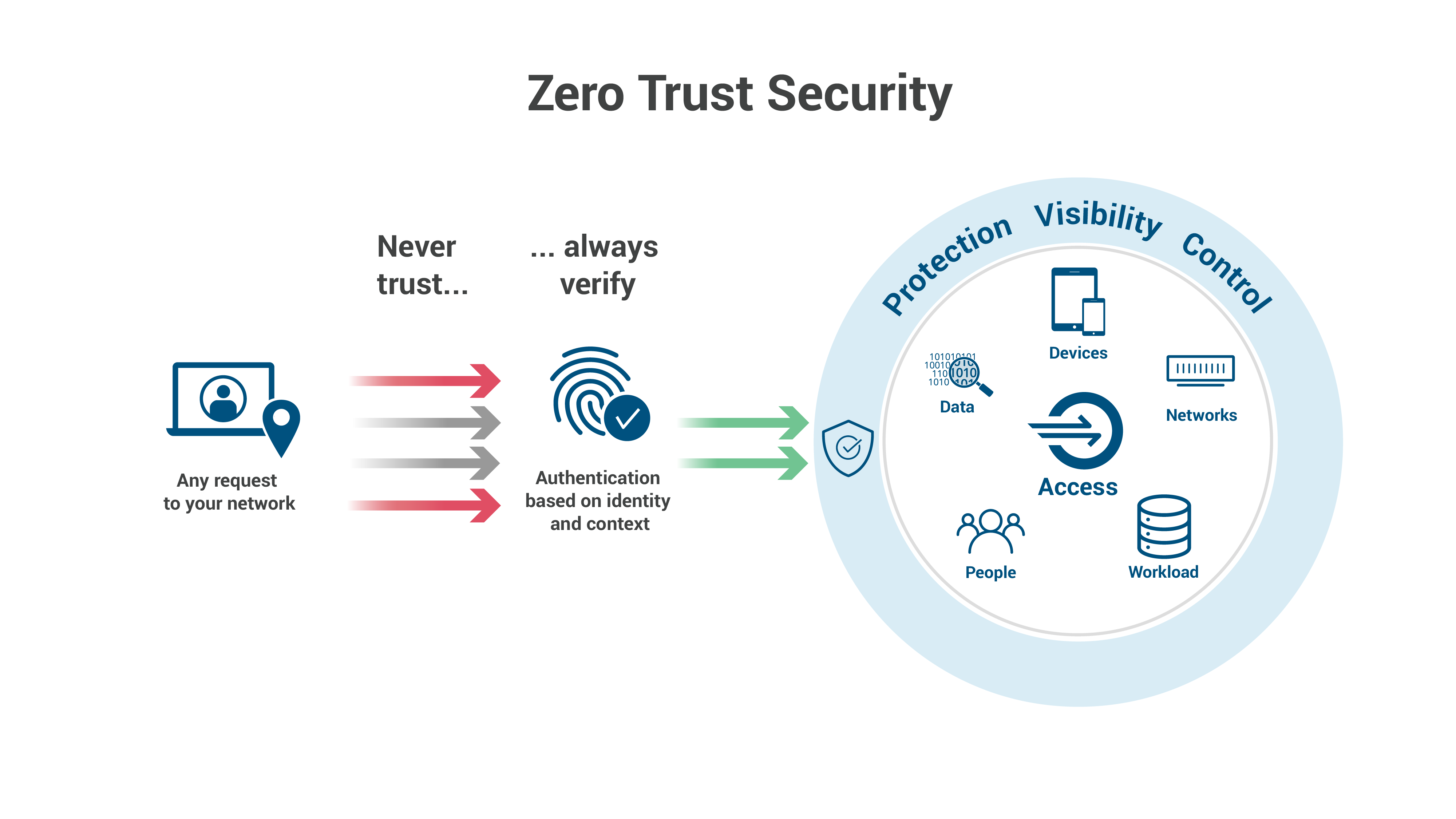
Emerging Trend 2: Zero Trust Architecture
Zero Trust Architecture is a security model that assumes breaches and verifies each request as though it originates from an open network, enhancing security by minimizing trust and continuously verifying access.
Conclusion: Reinforcing Key Value Proposition
Implementing robust business cybersecurity solutions is essential for protecting your business from evolving threats. By following best practices and staying informed about emerging trends, businesses can build a secure and resilient infrastructure that adapts to their evolving needs.
Call to Action: Contact our team of experts at Movantech Systems to discuss how we can help you implement comprehensive cybersecurity solutions tailored to your business goals.
Take the first step towards a secure and protected future today!


